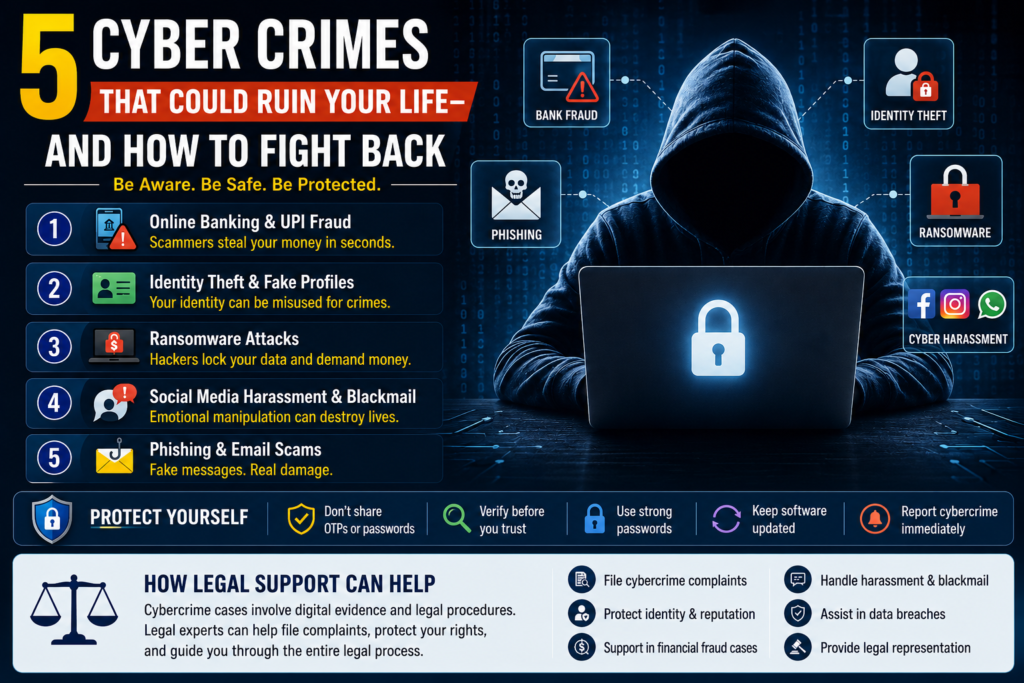
In today’s digital world, cybercrime is no longer limited to large corporations or tech experts. Ordinary people, students, working professionals, business owners, and senior citizens are increasingly becoming victims of online fraud and cyber attacks. A single fake link, suspicious call, or hacked account can result in financial loss, emotional trauma, identity theft, or legal complications. As cyber criminals continue using advanced techniques to target people online, awareness has become the strongest defense. Understanding how these 5 types of cyber crimes happen and knowing your legal rights can help you stay protected.
This guide explains five major cyber crimes that can seriously impact your life and how you can fight back with the right precautions and legal support.
Why Cyber Crime Is Rising in India
India’s growing digital ecosystem has made online transactions, social media usage, and internet banking more common than ever. While digital convenience has improved lives, it has also opened doors for cyber criminals.
Cyber attacks now target:
- Online banking users
- UPI payment users
- Social media accounts
- Business databases
- Smartphones and laptops
- Email accounts
- Personal identity documents
Many victims lose money or sensitive information simply because they are unaware of modern cybercrime tactics.
1. Online Banking and UPI Fraud
How Online Financial Frauds Happen
UPI and online banking scams are among the fastest-growing cyber crimes in India. Fraudsters often impersonate:
- Bank officials
- Customer support executives
- Delivery agents
- Loan providers
- KYC verification teams
They manipulate victims into sharing:
- OTPs
- ATM PINs
- UPI credentials
- Screen-sharing access
- Banking passwords
In many cases, scammers create panic by claiming accounts will be blocked immediately.
Red Flags You Should Never Ignore
Be alert if you receive:
- Calls asking for OTPs
- Unknown QR codes for receiving money
- Suspicious payment requests
- Fake bank messages
- Links asking you to update KYC details
How to Protect Yourself
- Never share OTPs or passwords
- Avoid clicking unknown links
- Verify bank-related calls directly
- Use secure banking apps only
- Enable two-factor authentication
Legal Support for Victims
Victims of banking fraud should immediately:
- Inform their bank
- Freeze affected accounts
- File a cybercrime complaint
- Preserve transaction evidence
Consulting a qualified Cyber Crime Advocate can help victims take legal action quickly and improve the chances of recovering losses.
2. Identity Theft and Fake Social Media Profiles
What Is Identity Theft?
Identity theft occurs when criminals steal your personal information and misuse it online. This may involve:
- Creating fake social media accounts
- Taking loans using your documents
- Misusing Aadhaar or PAN details
- Conducting scams in your name
Victims often face reputational damage and financial stress.
How Cyber Criminals Steal Identities
Attackers collect information through:
- Phishing websites
- Data breaches
- Fake job portals
- Malware attacks
- Social media scraping
Even publicly shared photos and information can be exploited.
How to Stay Safe Online
- Limit personal information on social media
- Use strong and unique passwords
- Regularly monitor bank statements
- Enable account privacy settings
- Avoid uploading sensitive documents online
Legal Remedies Available
Victims can seek legal assistance to:
- Remove fake profiles
- File police complaints
- Protect digital reputation
- Prevent further misuse of identity
Experienced cyber law professionals can guide victims through legal procedures and digital evidence collection.
3. Ransomware Attacks
What Is Ransomware?
Ransomware is a serious cyber attack where hackers lock or encrypt files and demand money to restore access. These attacks commonly target:
- Businesses
- Hospitals
- Educational institutions
- Freelancers
- Individuals storing sensitive data
Victims suddenly lose access to important files, documents, and systems.
Common Ways Ransomware Spreads
Ransomware usually enters through:
- Fake email attachments
- Pirated software
- Unsafe downloads
- Weak passwords
- Infected websites
One careless click can compromise an entire network.
Prevention Tips
- Back up important data regularly
- Keep software updated
- Use trusted antivirus protection
- Avoid downloading unknown files
- Use secure internet connections
What Victims Should Do
If attacked:
- Disconnect infected devices immediately
- Avoid paying hackers
- Contact cyber security expert
- Report the incident officially
- Seek legal assistance
Prompt action can help minimize further damage.
4. Social Media Harassment and Cyber Blackmail
The Growing Threat of Online Harassment
Cyber harassment has become a major concern, especially on social media platforms. Criminals misuse personal photos, videos, and private chats for:
- Blackmail
- Threats
- Stalking
Women, students, and professionals are among the most affected groups.
How Cyber Blackmail Works
Attackers often pretend to be:
- Friends
- Romantic partners
- Influencers
- Recruiters
After gaining trust, they manipulate victims emotionally and later threaten them using personal content.
How to Protect Yourself
- Avoid sharing sensitive content online
- Reject suspicious friend requests
- Keep accounts private
- Block abusive users immediately
- Be cautious during video calls with strangers
Legal Help for Victims
Victims should:
- Preserve screenshots and evidence
- Report fake or abusive accounts
- File cybercrime complaints
- Consult a cyber law advocate immediately
Professional legal guidance can help remove harmful content and protect victims from further harassment.
5. Phishing and Email Scams
What Is Phishing?
Phishing is a cyber attack designed to trick people into revealing confidential information through fake:
- Emails
- SMS messages
- Websites
- Social media messages
These scams are designed to look genuine and trustworthy.
Common Phishing Examples
Cyber criminals may send:
- Fake banking alerts
- Income tax refund messages
- Delivery notifications
- Job opportunities
- Investment offers
- Password reset emails
The objective is to steal sensitive information.
How to Identify Phishing Attempts
Watch for:
- Unknown senders
- Suspicious links
- Urgent requests
- Poor grammar
- Requests for personal data
Always verify before responding.
Best Ways to Stay Protected
- Never click unknown links
- Use spam protection tools
- Enable multi-factor authentication
- Verify website URLs carefully
- Educate family members about scams
Awareness is one of the strongest protections against phishing attacks.
How a Cyber Crime Advocate in Telangana Can Help
Cybercrime cases often involve technical evidence, digital investigations, and legal procedures that can overwhelm victims. A knowledgeable Cyber Crime Advocate in Telangana can assist with:
- Filing cybercrime complaints
- Legal notices and representation
- Financial fraud recovery guidance
- Social media harassment cases
- Data theft and privacy violations
- Identity theft disputes
- Digital evidence handling
Professional legal support can make the process faster, more effective, and legally stronger.
FAQ’s
1. What should I do immediately after becoming a victim of cybercrime?
Block affected bank accounts or cards
Change passwords
Preserve screenshots and evidence
Report the incident to the cybercrime portal
Consult a cyber law advocate
Quick action can reduce financial and legal damage.
2. Can stolen money from online fraud be recovered?
3. How can I file a cybercrime complaint in Telangana?
4. What evidence should I save in a cybercrime case?
Screenshots
Emails
Phone numbers
Transaction receipts
Chat conversations
Payment details
URLs and profile links
Digital evidence is crucial for legal action.